Introduction to multi-cloud security
As multi-cloud adoption continues to grow, so does the need for effective security measures. Multi-cloud environments can be complex and difficult to secure, but there are a few key considerations that can help make your architecture more secure.
In this section, we’ll cover the basics of multi-cloud security and introduce some of the best practices for securing your environment. We’ll also touch on some of the challenges you may face when securing a multi-cloud environment.
Understanding the challenges of multi-cloud environments
Multi-cloud environments are becoming increasingly popular as organizations look to take advantage of the benefits of different cloud providers. However, multi-cloud environments can be complex and challenging to manage. In order to effectively secure a multi-cloud environment, it is important to understand the challenges and how to mitigate them.
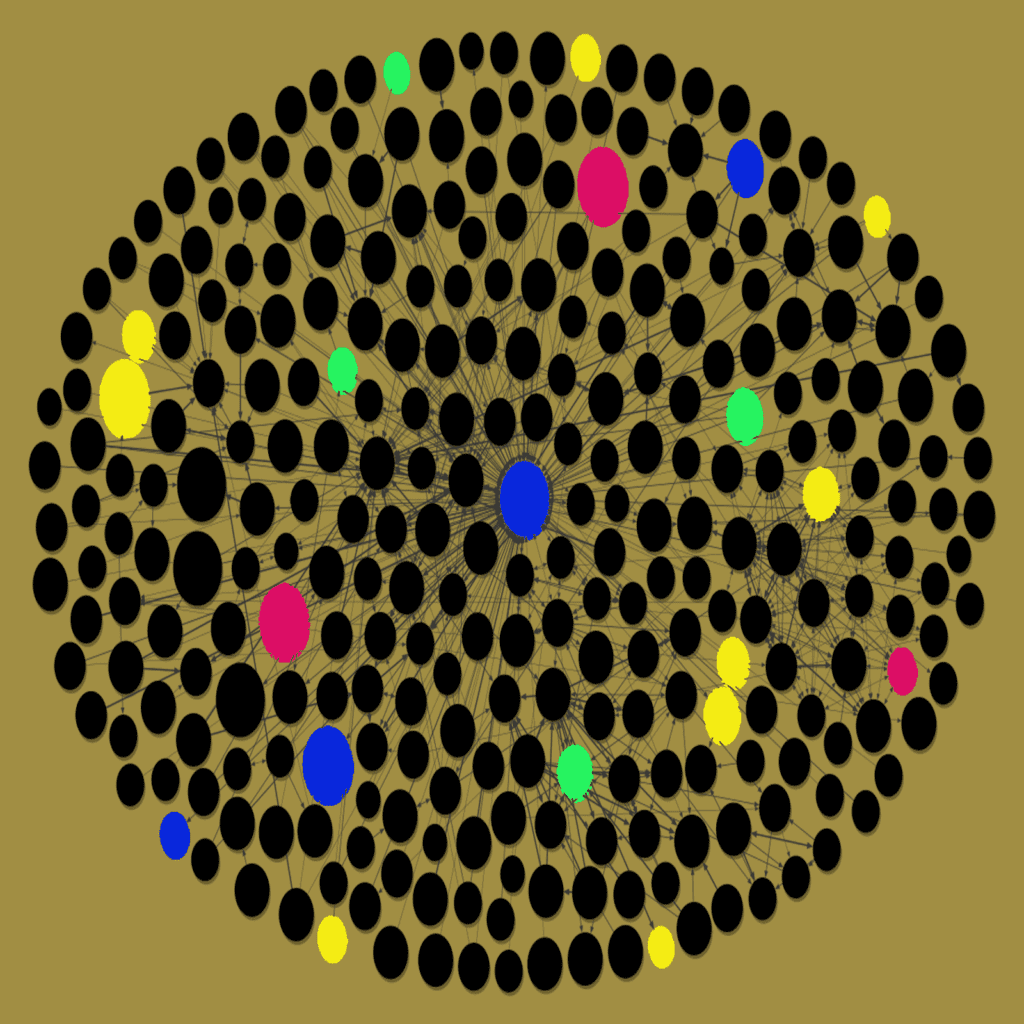
One of the biggest challenges of multi-cloud environments is managing security and compliance across multiple cloud providers. Each cloud provider has its own security controls and policies, which can make it difficult to ensure consistency across the environment. Additionally, data in a multi-cloud environment is often spread across multiple locations, which can make it difficult to protect.
Another challenge is managing cross-provider dependencies. When using multiple cloud providers, there can be dependencies on services from other providers. For example, if an application is hosted on Amazon Web Services (AWS) but uses a database hosted on Microsoft Azure, there is a dependency on both AWS and Azure. If one of these services goes down, it can impact the availability of the other service.
Finally, cost management can be a challenge in a multi-cloud environment. Organizations need to carefully track usage across all of their cloud providers in order to avoid overspending. It can also be difficult to compare pricing between different providers, as they all have different pricing models.
Despite these challenges, multi-cloud environments offer many benefits and can be effectively secured with careful planning and execution. By understanding the challenges and taking steps to mitigate them, organizations can take advantage of the benefits of multi-cloud environments.
Key components of a secure multi-cloud architecture

There are three key components to a secure multi-cloud architecture: data security, identity and access management, and network security.
Data Security
The first step to securing your data is to encrypt it. All data should be encrypted at rest and in transit. This includes data stored in the cloud as well as data moving between different cloud providers. In addition to encryption, you should also consider implementing other security measures such as data loss prevention (DLP) and intrusion detection/prevention (ID/IP).
Identity and Access Management
The second key component of a secure multi-cloud architecture is identity and access management (IAM). IAM provides the controls needed to ensure that only authorized users have access to your cloud resources. It also helps to prevent unauthorized access to sensitive data. Implementing IAM can be complex, but there are several managed services that can help simplify the process.
Network Security
The third key component of a secure multi-cloud architecture is network security. Network security is important for both preventing unauthorized access to your cloud resources and ensuring that data remains confidential while in transit. When configuring network security, you should consider using firewalls, VPNs, and other security tools such as intrusion detection/prevention systems (IDS/IPS).
Best practices for multi-cloud security design
Most organizations now operate in a multi-cloud environment, using a mix of on-premises, private, and public clouds. While the benefits of multi-cloud are clear, the security challenges are substantial. A comprehensive security strategy is essential to securing your multi-cloud environment.
Here are some best practices for designing a secure multi-cloud architecture:
1. Implement a centralized cloud management platform: A centralized cloud management platform can help you gain visibility into all your cloud assets and activity, across all accounts and providers. This visibility is critical for effective security monitoring and incident response.
2. Define and enforce security policies: Security policies should be centrally defined and enforced across all your cloud environments. These policies should be tailored to your specific business needs and requirements.
3. Use identity and access management (IAM) controls: IAM controls help you manage who has access to what data and resources in your cloud environment. By properly configuring IAM controls, you can limit access to only those who need it, helping to reduce the risk of data breaches.
4. Encrypt data at rest and in transit: Data encryption is an essential part of any security strategy, but it’s especially important in cloud environments where data is often stored outside of your direct control. Make sure to encrypt all sensitive data both at rest and in transit, using strong encryption algorithms such as AES 256-bit encryption.
5. Implement comprehensive monitoring: Comprehensive monitoring is essential for detecting and responding to potential threats in a timely manner. Make sure to monitor all aspects of your cloud environment, including user activity, system logs, and resource utilization.
6. Use a secure development process: Secure coding practices should be followed when developing applications in the cloud. This includes following best practices such as testing, logging, and input validation.
7. Use security tools and services: There are many security tools and services available to help secure multi-cloud environments. These include offerings from the major cloud providers as well as third-party vendors. A layered approach to security is usually best, so make sure to leverage multiple tools and services where appropriate.
Implementing secure access management in multi-cloud environments
Organizations are increasingly using multiple cloud service providers to take advantage of the benefits each provider offers. However, this can create security and compliance risks if not managed properly.
A multi-cloud security strategy should include secure access management to control who has access to which resources and data. This can be implemented using a central identity and access management (IAM) system that integrates with the different cloud environments.
IAM can provide Single Sign-On (SSO) capabilities so users only need to remember one set of credentials, as well as role-based access control (RBAC) to ensure that users only have the permissions they need to do their job. IAM can also help prevent data leakage by providing activity logging and auditing capabilities.
Organizations should also consider implementing a unified security policy across all their cloud environments. This will help ensure consistent enforcement of security controls regardless of where data is stored or accessed.
By implementing these strategies, organizations can securely take advantage of the benefits of multi-cloud environments while minimizing the risks.
Protecting multi-cloud data and storage
Multi-cloud environments are becoming increasingly popular as businesses look to take advantage of the benefits of different cloud providers. However, this can also create security challenges, as data and storage spread across multiple clouds can be difficult to protect.
There are a few key things to consider when it comes to protecting multi-cloud data and storage:
Encryption is critical for protecting data at rest and in transit. All data should be encrypted, whether it is stored on-premises or in the cloud.
Access control is another important consideration. Make sure that only authorized users have access to data, and that access levels are properly configured.
Monitoring and auditing are essential for identifying potential threats and catching them before they cause damage. Regularly review logs and other security data to look for suspicious activity.
In addition to these general security measures, it is also important to consider the specific security capabilities of each cloud provider you use. Make sure that you understand how each provider secures data, and choose the one that offers the best protection for your needs.
Compliance and regulatory considerations for multi-cloud security
When it comes to multi-cloud security, compliance and regulatory considerations are key. Here are some things to keep in mind:
-Data sovereignty: Where is your data being stored? Is it compliant with regulations in your country?
-Jurisdiction: What laws apply to your data? Make sure you understand the implications of storing data in different countries.
-Encryption: All data should be encrypted, both at rest and in transit. This is especially important if you are using a public cloud provider.
-Access control: Who has access to your data? Make sure you have strict controls in place to prevent unauthorized access.
-Auditing: You need to be able to track who is accessing your data and when. This is important for compliance and troubleshooting purposes.
Enhancing multi-cloud security through automation and AI
The multi-cloud approach has become increasingly popular in recent years as organizations seek to take advantage of the benefits of different cloud platforms. However, this can also create new security challenges, as each platform has its own security controls and processes.
Automation and artificial intelligence (AI) can help to address these challenges by providing a way to centrally manage security across multiple cloud platforms. Automation can help to identify and address potential security issues before they cause problems, while AI can be used to detect and respond to threats in real time.
Together, these technologies can provide a powerful solution for securing multi-cloud environments. By using automation and AI to proactively manage security, organizations can reduce the risk of data breaches and other security incidents.
Continuous improvement of multi-cloud security
In order to ensure the security of data and applications in a multi-cloud environment, it is important to continuously monitor and improve security measures. This includes regularly assessing risks, implementing security controls, and monitoring compliance.
Organizations should also have a clear understanding of the different types of threats that exist in the cloud and how to mitigate them. Additionally, they should have a plan in place for responding to incidents quickly and effectively.
Conclusion and final thoughts on securing multi-cloud environments
Multi-cloud environments are becoming increasingly popular as businesses strive to improve agility, flexibility, and scalability. However, these benefits come at a price – multi-cloud architectures can be complex and difficult to secure. In this article, we’ve discussed some of the challenges involved in securing multi-cloud environments and offered some recommendations for overcoming these challenges.
Overall, the key to effectively securing multi-cloud environments is careful planning and execution. By taking the time to understand the risks involved and put in place the appropriate controls, organizations can minimize the likelihood of security incidents occurring.